Modern Reconnaissance Techniques. How Threat Actors Gather Information You Thought Was Private
"You’ve already been hacked."That’s what it can feel like when you learn how much an attacker can discover about your organization before they even launch a single exploit.
- Apr 13, 2026

"You’ve already been hacked."
That’s what it can feel like when you learn how much an attacker can discover about your organization before they even launch a single exploit. The truth is, modern cyberattacks rarely start with malware deployment or network intrusion, they start with reconnaissance. And in today’s hyper-connected world, your company’s public footprint is often far larger than you think.
Attackers can map your digital presence in detail: employee names, email patterns, exposed development environments, forgotten cloud storage, outdated applications, and even subtle indicators buried in press releases or job postings. These breadcrumbs form a blueprint of your operations, letting attackers choose the easiest and most profitable entry points.
For businesses, especially those operating with distributed teams, complex application stacks, and a sprawling cloud footprint, ignoring reconnaissance means ceding the first and often decisive move to the attacker. This is where Ebryx’s Vulnerability Assessment and Penetration Testing (VAPT) service plays a critical role, simulating adversarial recon before the real adversary gets there.
Reconnaissance 101: The First Phase of Modern Attacks
What is Reconnaissance in Cybersecurity?
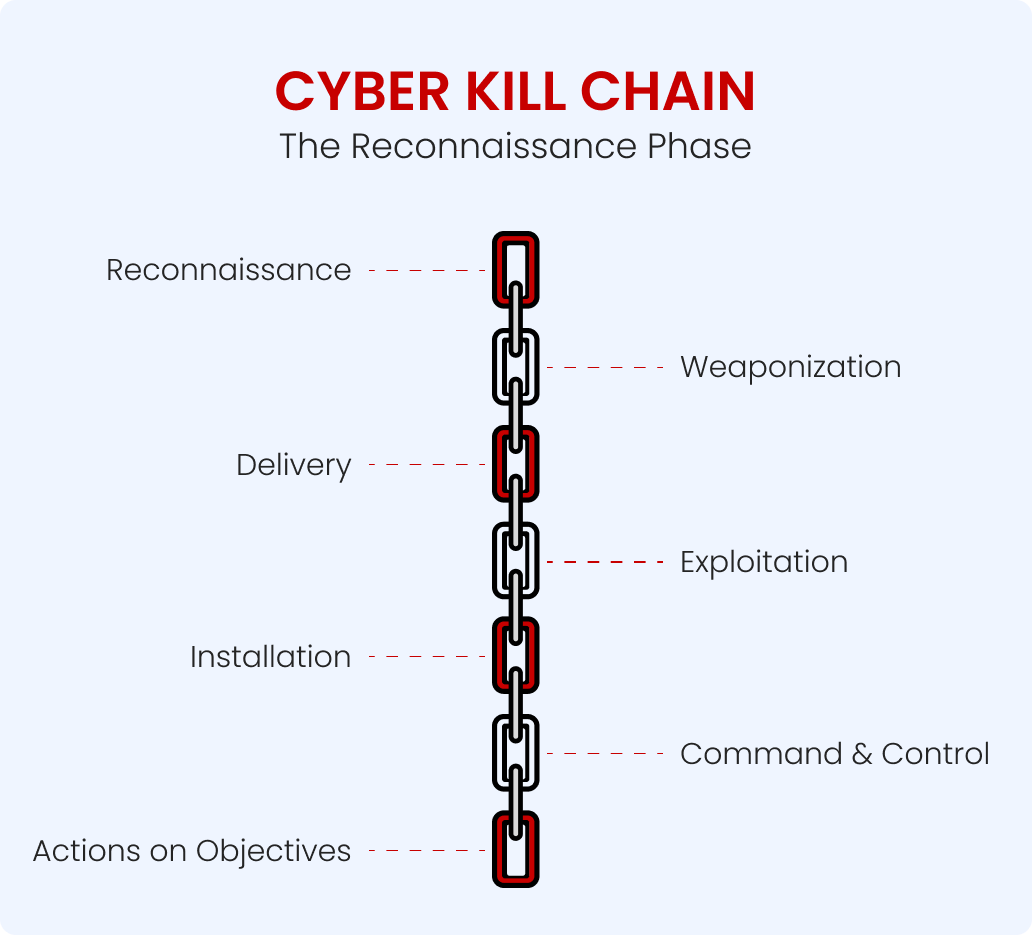
Reconnaissance (or “recon”) is the process of gathering intelligence about a target environment without directly breaching it yet. Think of it as the mapping stage of a military campaign. Before an army moves in, it must understand the terrain, the enemy’s strengths and weaknesses, and the best approach for an attack.
In a cyber context, this includes cataloging IP addresses, identifying exposed services, fingerprinting web technologies, profiling key employees, and uncovering forgotten or poorlysecured assets. Reconnaissance informs not only if an attack is possible but also how it should be executed for maximum impact.
Why It Matters for Businesses
Organizations often underestimate how much can be learned without breaching their perimeter. Public code repositories, unsecured APIs, abandoned subdomains, and even LinkedIn posts can give adversaries actionable intelligence.
For example:
- A misconfigured staging environment can reveal API keys and database schemas.
- An outdated WordPress plugin in a blog subdirectory might serve as the perfect beachhead.
- An employee’s public GitHub repo could accidentally contain production secrets in commit history.
Attackers thrive on such details. The better their recon, the more surgical and successful their attacks.
Passive vs Active Reconnaissance
Passive Reconnaissance
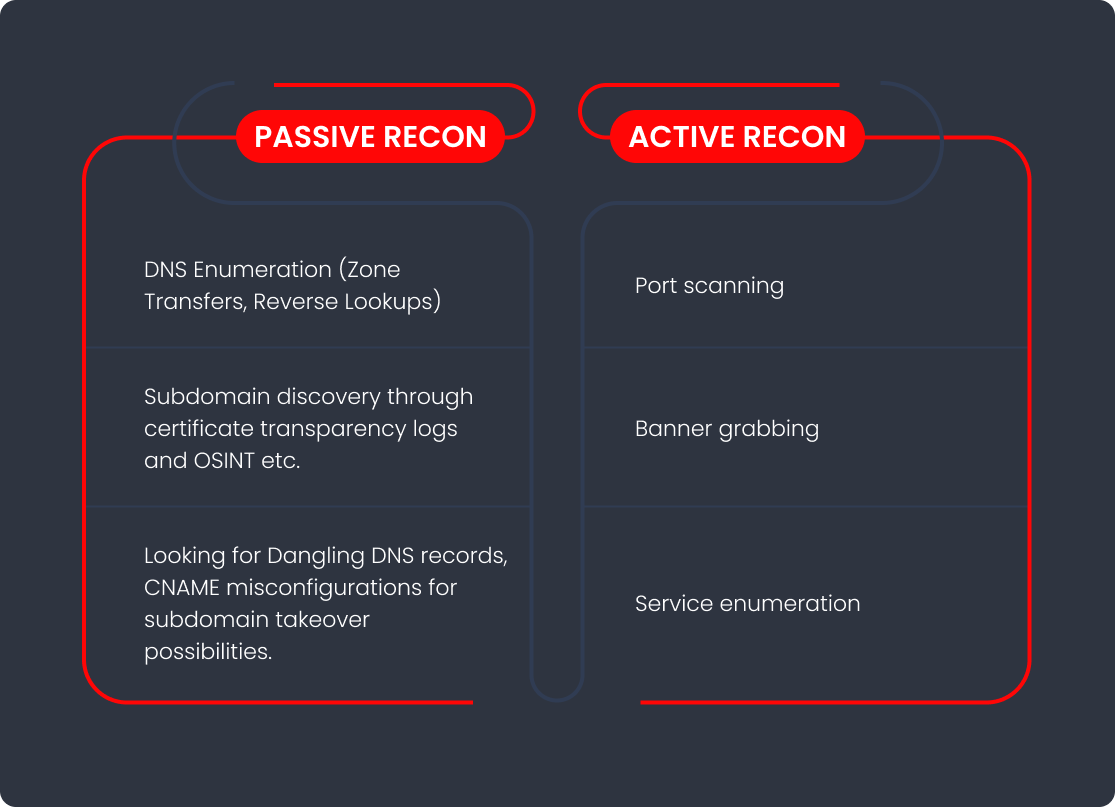
Passive recon involves collecting data without directly interacting with the target in a detectable way. This might include:
- Mining WHOIS data
- Scraping social media for employee details
- Using Shodan to find exposed devices
- Reviewing job postings for technology stack clues
Since no direct requests are sent to the target infrastructure, passive recon is stealthy and hard to detect, making it a preferred first step for advanced adversaries.
Active Reconnaissance
Active recon, on the other hand, involves directly probing the target environment to elicit responses that reveal vulnerabilities or configurations. This includes:
- Port scanning
- Service enumeration
- Banner grabbing
- Test exploitation in controlled scenarios
While active recon can yield richer detail, it’s more likely to trigger security alerts, unless, of course, your detection capabilities are inadequate.
Simple Analogy for Leaders
If passive recon is like studying blueprints from a public archive, active recon is like rattling the doors and windows to see which ones open. Both give valuable information but the latter risks being noticed.
Tools & Tactics Attackers Use
What is OSINT in the Cyber Context?
Open-Source Intelligence (OSINT) refers to collecting data from publicly available sources. In cybersecurity, OSINT feeds into reconnaissance by helping attackers' piece together seemingly harmless fragments into a coherent picture of your infrastructure.
Common Tools in Attacker Recon
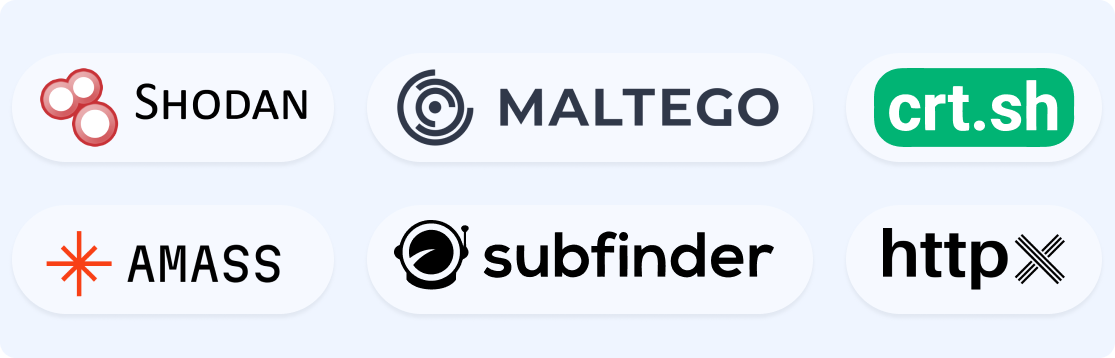
Some of the most popular tools in a threat actor’s recon toolkit include:
- Shodan – Search engine for internet-connected devices.
- theHarvester – Gathers emails, subdomains, and hostnames from public sources.
- Recon-ng – Framework for automated OSINT gathering.
- Maltego – Relationship mapping for entities and infrastructure.
- Amass – Comprehensive subdomain enumeration.
- FOCA – Extracts metadata from public documents.
Advanced actors also employ custom scripts and cloud-native scanning tools to bypass detection and avoid rate limits.
Key Insight
Alarmingly, Cloud security statistics indicate that 89% of businesses impacted by cloud misconfigurations were startups.
The sophistication of recon tools means that even minor, unmonitored changes, like a developer spinning up a temporary test environment, can expose sensitive data at scale. If you’re not actively discovering these exposures yourself, someone else likely is.
Common Recon Findings Across the Industry
Exposed Development or Test Environments
Test environments are notorious for being left unpatched, lacking authentication, and containing real data cloned from production. These become low-hanging fruit for attackers, offering them a playground to reverse-engineer applications without raising alarms.
Outdated Public-Facing Applications
Legacy applications, especially those with known CVEs, are magnets for automated scans. Attackers will often catalog these during recon and wait until they have a complete picture before striking.
Employee Data Enabling Targeted Attacks
Information about key personnel; roles, emails, project names, enables spear-phishing and business email compromise (BEC) campaigns. Developers revealing tech stack details in conference talks or code snippets on GitHub further enrich attacker intelligence.
Unprotected Cloud Buckets
Misconfigured AWS S3, Azure Blob, or Google Cloud Storage buckets remain a goldmine for attackers, often containing backups, logs, or sensitive configuration files.
Why This Should Alarm Senior Leadership
Executive & Brand Risks
88% of all data breaches originate from employee mistakes, underscoring how critical internal vigilance is for enterprise security. When an attacker identifies exploitable weaknesses in your infrastructure or brand presence, the attack surface includes not only systems but also the executive leadership’s reputation. Compromising a CEO’s email or hijacking a verified social account can lead to instant brand damage.
Legal & Compliance Consequences
Data exposure, even without a confirmed breach, can trigger compliance failures under GDPR, HIPAA, PCI-DSS, and other regulatory frameworks. A recon finding today could be a legal nightmare tomorrow.
Reputational Damage Without a Breach
Even if no data is stolen, public knowledge of exposed systems can erode customer trust. Security lapses, real or perceived can be amplified quickly in the media.
Stopping the Attack Before It Starts
Reducing the Public Attack Surface
This involves continuously discovering, classifying, and hardening internet-facing assets. In practice, it means:
Legal & Compliance Consequences
Data exposure, even without a confirmed breach, can trigger compliance failures under GDPR, HIPAA, PCI-DSS, and other regulatory frameworks. A recon finding today could be a legal nightmare tomorrow.
Reputational Damage Without a Breach
Even if no data is stolen, public knowledge of exposed systems can erode customer trust. Security lapses, real or perceived can be amplified quickly in the media.
- Regular DNS sweeps for subdomains
- Removing or securing unused endpoints
- Applying strict access controls to all environments
Securing Forgotten or Shadow Assets
Shadow IT systems created outside official IT governance, often bypasses security controls. These can include rogue cloud instances, unsanctioned SaaS tools, and side projects by development teams.
VAPT as the Pre-Attack Detection Tool
Ebryx’s VAPT service simulates real-world adversarial recon to uncover what attackers would find, before they do. This includes both passive OSINT collection and active probing, all in a controlled, ethical manner.
How VAPT Neutralizes Recon Advantages
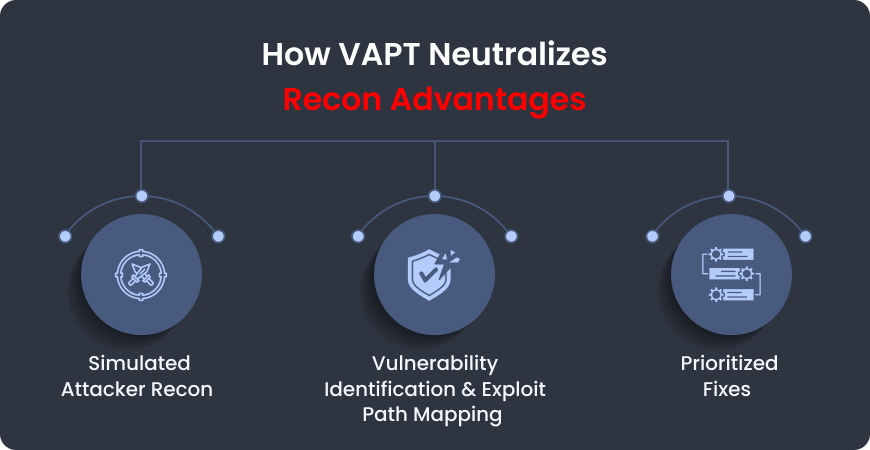
Simulating Attacker Recon
Ebryx’s security engineers replicate the mindset and approach of sophisticated threat actors to map your exposed footprint. This safe simulation reveals what an attacker’s first step might uncover, without exposing operational specifics, allowing you to address risks before they can be exploited.
Prioritizing Fixes with Context
The VAPT process doesn’t just produce a list of vulnerabilities; it contextualizes them. For example, an outdated service running on a forgotten subdomain might be prioritized higher if it also leaks API keys in its HTML source.
Example Scenario
Imagine a fintech company with:
- An unmonitored test API endpoint leaking customer transaction data formats.
- A Jenkins build server exposed on the public internet.
- Employee email addresses harvested from public GitHub commit logs.
In a real attack, an adversary could piece these elements together into a targeted intrusion. Ebryx’s VAPT would flag each exposure, provide the technical exploit path, and recommend remediation, closing the window of opportunity before the attacker makes their move.
Conclusion
Modern reconnaissance is silent but deadly. It’s not the flashy zero-day exploit or the headline-grabbing ransomware that first compromises your business, it’s the quiet, meticulous data gathering that makes those attacks possible in the first place.
Ebryx’s VAPT services combine thorough vulnerability assessments with advanced penetration testing to give organizations far more than a static list of issues. Our approach delivers a roadmap to resilience, simulating real-world adversary behavior to uncover weaknesses, demonstrate how they could be exploited, and provide actionable remediation guidance.
This means we don’t just scan for vulnerabilities, we actively validate them, chaining exposures together exactly as a determined attacker would. The result is a prioritized, context-rich picture of your true risk posture. By doing this preemptively, we help you close the gaps before threat actors can leverage them, turning every recon advantage they might have into a dead end.
The takeaway for senior leadership and technical decision-makers is simple: you can’t protect what you don’t know is exposed. Reconnaissance is inevitable. Whether the first recon sweep is conducted by an attacker or by your own trusted security team is entirely up to you.

.png)

.png)
